Future of Security (hint: Cloud)

SecurID
Can the enterprise spend enough money to truly secure itself?
As anyone following security (cloud security in my case) would know, the recent SecurID breach marked a transition for the security industry as a whole. RSA’s Executive Chairman Art Coviello wrote in an open letter on the company’s website and published in their 8-K SEC filing that hackers had mounted an “extremely sophisticated cyber attack” that has put at risk its SecurID product.
Epsilon
Then this morning, I receive the following email from my primary credit card company, Chase:
“Chase is letting our customers know that we have been informed by Epsilon, a vendor we use to send e-mails, that an unauthorized person outside Epsilon accessed files that included e-mail addresses of some Chase customers. We have a team at Epsilon investigating and we are confident that the information that was retrieved included some Chase customer e-mail addresses, but did not include any customer account or financial information. Based on everything we know, your accounts and confidential information remain secure. As always, we are advising our customers of everything we know as we know it, and will keep you informed on what impact, if any, this will have on you.
We apologize if this causes you any inconvenience. We want to remind you that Chase will never ask for your personal information or login credentials in an e-mail. As always, be cautious if you receive e-mails asking for your personal information and be on the lookout for unwanted spam. It is not Chase’s practice to request personal information by e-mail.
As a reminder, we recommend that you:
- Don’t give your Chase OnlineSM User ID or password in e-mail.
- Don’t respond to e-mails that require you to enter personal information directly into the e-mail.
- Don’t respond to e-mails threatening to close your account if you do not take the immediate action of providing personal information.
- Don’t reply to e-mails asking you to send personal information.
- Don’t use your e-mail address as a login ID or password.
The security of your information is a critical priority to us and we strive to handle it carefully at all times. Please visit our Security Center at chase.com and click on “Fraud Information” under the “How to Report Fraud.” It provides additional information on exercising caution when reading e-mails that appear to be sent by us.”
GoGrid
A week ago I received this email from my local cloud infrastructure provider:
“Dear Valued Customer:
In the normal process of reviewing our system activity, our Security Team discovered that an unauthorized third party may have viewed your account information, including payment card data. We immediately took action to protect our customers, including notifying federal law enforcement authorities, who have since seized the computing equipment and records of the single individual suspected of this misconduct. The criminal investigation is ongoing, and we will continue to assist the authorities in working toward a successful prosecution.
The security and reliability of our platform is fundamental to our business, as is the trust and faith that our customers place in us. We have completed a rigorous audit conducted by a leading security firm. There were three important findings that lead us to believe the situation has been contained:
1. The method utilized by the suspect to gain access has been identified and remediated.
2. It appears that the suspect’s sole motive was to acquire free services from us. We have no evidence suggesting that the suspect was targeting customer infrastructure or payment cards.
3. We have no indication that any customer information was shared with any other unauthorized parties or that there has been unauthorized use of any cardholder’s data.
In addition, we are instituting a series of new measures designed to further enhance security. Any information that you may need in order to comply with these measures will be communicated through the user portal and the support ticketing system. As an added precaution, affected cardholders will receive a letter in the mail offering credit monitoring services at our expense.
Client privacy, confidentiality and security are central to us. We greatly value your business and apologize for any inconvenience this causes. If you have any questions related to any of the above, please contact our Customer Service Team at 1-866-310-8477 or 1-415-963-9955 or via email at gogridteam@gogrid.com.”
Is 2011 the “Year of Breaches”??
So What’s The Future?
I would argue that the Advanced Persistent Threats are going to make it IMPOSSIBLE to build a Cheyenne Mountain of security around your enterprise…..from the perspective that attack groups (not individuals, but rather organized intelligent and well-funded teams) are sophisticated AND from the perspective that it’s a matter of economics!!!
Sure, you can buy a $150K CISCO ASA 5500 series Intrusion Protection System that sits on your network providing a Cheyenne-level of protection for 10Gbps of your most critical assets, aka data. Yes, it has support for over 25,000 threats and supposedly a day-zero protection with anomaly detection.
But doesn’t this beg the question, “Do you think companies like RSA, Chase, or GoGrid, having security devices which have similar specs as the 5585 SSP-60 IPS threat-eating dragon?” I’m sure they do. So what’s the problem?
The problem is best represented by a quote from one of my super-secret, government security guys (someone who doesn’t have a Facebook or Linkedin account…if you entered in his name into Google, you will only find others who have similar names)…he said, “Jim, there is no such thing as 100% security…or even something close. You’d be surprised the poor level of security at some governments agencies I service. It comes down to economics. You have to pay A LOT to increase your security, and even then if you are the target of an APT, it’s only a matter of time.”
I suppose knowing that an attack costs $204 per data record, or $6.75M per incident on average (per the Ponemon Institute), you can simply do the math to determine what you should be spending.
But what if you find out that no matter how much you spend to protect, there isn’t a wall big or strong enough between the bad guys and your personal data….then what is the future of security?
IBM says it that it monitors 13 billion real-time security events every day for more than 4,000 clients. That’s about 3 million events per client per day….or as a whole, 150,000 events per second.
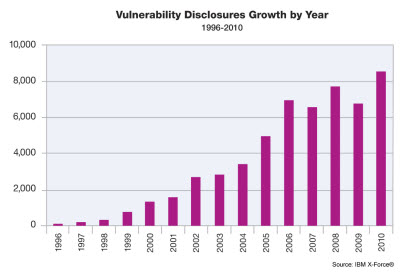
IBM found that there were 8,000 new web vulnerabilities discovered during 2010, up 27 percent from 2009.
Tom Cross from IBM’s X-Fource group talks about how vulnerabilities are only getting worse due to the growing number of hand-held and mobile devices used in the workforce, here. How about the growing reliance on cloud (SaaS, PaaS, and IaaS). Talk to Jim Reavis, head of the Cloud Security Alliance to find out that when Analysts say that security is the biggest concern over public cloud…well, it’s true.
Internet vs. Intranet
The boundaries of the enterprise are now non-existent. I don’t mean that there’s no need for firewalls….but that the many new SaaS offerings offered today have leveraged the Internet to provide cloud applications which were once hosted on your Intranet. There’s a blurring of the lines between Intranet and Internet applications.
This means that enterprises will operate and interact with more than one cloud environment. There will be hosted application clouds, infrastructure clouds, web hosting clouds, etc. Each of these cloud environments will present potentially new vulnerabilities that hackers will attempt to exploit in pursuit of the data each holds and we’ll need a well thought out threat-based protection model to address them well.
Then the regulatory environment will make deployment of comprehensive cloud based data protection systems not just a business imperative, but also a legal one. Even if your business isn’t covered by the existing requirements of HIPAA, SB-1386, Sarbanes-Oxley, or the EU Privacy Directive, you certainly will have new compliance requirements emerge from the data protection legislation pending in the U.S. Congress.
Ultimately, we’ll need to have some sort of global trust system in place which not only allows each of these entities to authenticate their identity and veracity to one another in support of each interaction and transaction, but monitors them after authentication is made.
Data Protection Systems with Jurisdiction
If you have a responsibility for IT or hold a senior position in your organization, you have a responsibility to ensure that your data is stored in a jurisdiction that has data protection laws at least as strong as your current jurisdiction. Phil Dunkelberger (past CEO of PGP) and I met recently to discuss the state of the security industry. He consistently sends a clear message about the need for data-level protection which includes jurisdiction monitoring and control.
Device-level Trust System
It is generally understood that organizations cannot successfully defend against all cybersecurity attacks. Also, as the level of security is increased, so does the level of overhead and management that accompanies that security, number of vulnerabilities created by the organization, etc. So, while precautions must be taken to prevent such attacks, an equally important function is the discovery, investigation and understanding of network security breaches AFTER they happen so that they can be stopped, if still ongoing, and prevented in the future.
A time when you are 100% secure
It’s called “Time Zero”. When a new employee is hired (and a suite of devices allowed on the enterprise network), that person’s security level is the highest…at day zero, hour zero, minute zero (call this “Time Zero”). From that point on, that person (associated devices, access to data, etc.) have a “trust level” or security profile which will only degrade.
In addition, the data associated with that new employee and the data that the new employee gains access to is non-existant at Time Zero. Envision an environment where you capture detailed data on data created/accessed by the employee and the related connections that employee’s devices use to gain access to any/all data….all over time, you can use this detailed information to build a profile for every employee and every device.
Imagine the power associated with the ability to analyze streams of data associated with every connection, every data access made. Not only could you build a long-term statistical profile, but compare it to a near-term statistical profile and other employee/device profiles to determine anomalies which could be questioned, anomalies which could be used to fingerprint cybersecurity attacks, in a way which allows the organization to act BEFORE or ON zero-day….in real-time.
Are we capable of capturing such data for every user, every device, for every service used…whether on the Intranet or Internet? And if so, could we cost justify the storage, processing, and real-time reporting needed to make it valuable?