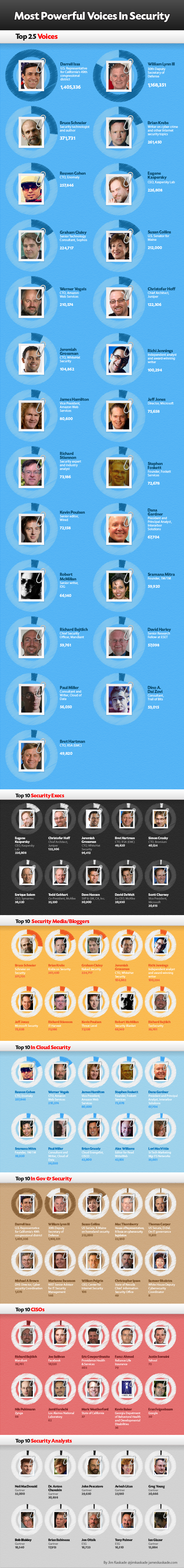
Top 25 Voices in Security
Reprinted from Sys-Con Media and Ulitzer.com.
The Security community has a growing number of influential and important people, especially as the industry rises to meet the need to address more advanced security threats, such as targeted attacks. But how does a company in the security industry truly identify the influential people? And then once identified, how does one use influential voices to help promote their brand? In this study, we answer the first question – how to identify the most powerful voices in your industry, focusing on the security space, and as part of this we provide you a list of people to follow for the best, most up to date information, and who have the loudest voices to help help carry some of your key messages. In a future study, we will discuss how to further exploit that knowledge to market your brand.
As executives in a fast-changing and social world, many of us struggle with the ability to have our voices heard by our target customers, especially as news in our industry is gaining more attention (e.g. a “hot space”). You would think that if you were a part of an emerging category, that people would pay attention to you. However, getting above the “noise” is a problem for some companies.
Until now we’ve found ourselves using traditional and often ineffective marketing and sales tools. With firms like Radian6, Eloqua, Marketo and the like, CMOs are being presented with new ways of leveraging social networks to understand, target, and reach their markets.
According to leading researchers, some individuals in your target industry have greater influence than others, holding a virtual megaphone powered by their social graph. The term “social graph,” coined a few years ago by Facebook CEO, Mark Zuckerberg, is also referred to as the “open graph,” and is used to describe an aggressive initiative to connect the dots between the relationships and associations built on Google+, Facebook, Twitter, Linkedin, Foursquare, other public social networking services, and emerging private enterprise social networks like Salesforce’s Chatter, Yammer, and others. Emerging companies like Klout also use the open graph to measure the number of people you reach, how much those people amplify your message, and ultimately the strength of your network.
When you look at established industries like Security, more well-known people, like executives of incumbent security companies, are considered the influencers, while others who are less known exist in niches in the blogosphere or in newly formed circles. Examples of niche groups might include the Cloud Security Alliance, or U.S. congressman Mac Thornberry’s Cybersecurity Task Force. You can argue that some people in these niche groups might not even be considered security “experts” or “thought leaders”. However, by being associated with an area which is highly visible from a security perspective (e.g. cloud), their voices can still carry significant weight.
Our thesis is that these smaller groups in security can have the most powerful voices. Collectively; however, ALL these groups consist of a number of the most vocal, most followed and re-posted commentators in the security community today. If you are involved in security (as a new startup or an established player), there are a select number of people you need to know.
In compiling our ranking of the Most Powerful Voices (“MPV”) in security, we took advantage of concepts similar to Google PageRank for people, working with researchers and thought leaders such as Mark Fidelman (see “The Most Powerful Voices in Open Source”).
The metrics needed to measure both broadcast power and profundity were identified through a number of studies performed across several industry categories. Although there have been many advancements in the area of social marketing, the work presented here still requires techniques not yet offered by any single social graph tool available today.
The MPV formula is based on “reach” by examining the number of followers and buzz an individual has on sites like Google and Twitter. We then determine how much impact an individual has with their followers and subscribers. We ask questions like: If you have a twitter account, how often are you uniquely referenced, or retweeted? How much buzz is created around your blog posts, tweets, Quora answers, Linkedin groups, and other messages? How often is an individual referenced in the blogosphere?
Top Executive Voices in Security
The MPV formula illustrates how much additional broadcast power an individual has versus an average active person (defined later). For example, Eugene Kaspersky, CEO of Kaspersky Lab, has 5,035 times more broadcast power reach than the average person, while Enrique Salem, CEO of Symantec, has a respectable 855 times more broadcast power than the average person. At the surface, security executives are good targets when searching for powerful voices. However, most, if not all, powerful executives are governed or constrained on what they can say. You won’t find CEOs of publicly traded companies providing transparent dialog about their opinions on controversial topics (although Leo Apotheker, CEO at HP, may prove me wrong on one or both of these points). In addition, it’s quite difficult to get executives to speak on your particular topic, or about your brand. [Note: We included Ex-CEO from McAfee, David DeWalt, because we assume we’ll hear of his next high-profile placement and we can update the company then].
Top Media/Blogger Voices in Security
Then there’s the power of active security bloggers like Bruce Schneier (“Schneier on Security”) who has a voice which is 8,252 times the average. Yes, that’s more than Eugene Kaspersky! Why? Because he’s willing to speak his mind on topics where people want transparent and insightful perspective. Also, a dialog can occur between the average person and a blogger. It’s easier to reach even the most well known bloggers or editors of news and media properties.
Top Voices in Cloud and Security
We looked at the top 100 voices in cloud computing and searched for those discussing security. Some voices were found to be as high as 5,700 times the average person. As an example, Reuven Cohen, founder and CTO of Enomaly, may not be solely focused on the security industry, but security is the number one issue when it comes to cloud adoption. So why is Reuven’s voice stronger than Eugene Kaspersky? We speculate that this is based on the fact that Reuven is a very ungoverned and vocal voice at an early-stage startup, and that the audience for these voices may assume that startups generally help define the trends and direction of the industry.
Top Government Leaders and Security
We debated whether to include government officials due to their more general public following. Government leaders have a much different audience than those following security executives. However, many government officials are actively involved in security. For example, Susan Collins, who is a ranking member of the Homeland security and Governmental Affairs Senate Committee, is a co-author of comprehensive cybersecurity legislation, which resulted in much debate in prominent media outlets such as Forbes and the Washington Post.
In addition, as we searched for people who are addressing topics in cyber security, we found people such as U.S. Representative for California’s 49th congressional district, Darrell Issa and, of course, the 30th Deputy Secretary of Defense, William Lynn III, who currently maintain voices 31,195 and 25,935 times that of the average person, respectively!
Therefore, we ultimately decided to include government officials because when they communicate they generate a lot of attention.
Chief Information Security Officers
Our survey of over 100 CISOs resulted in the top 10 voices exceeding 1,300 times that of the average person (e.g. See Mandiant CSO, Richard Bejtlich, and Facebook CISO, Joe Sullivan). CISOs or CSOs are prominent figures in the enterprise now. With the rise of advanced persistent threats (APTs), these executives are under growing pressure to lock down their company’s intellectual property. In our recent discussions with several Fortune 100 CISOs, some believe there are several APTs lying dormant and undetected in their enterprise today. Look at the recent example of a highly sophisticated and targeted attack on Google’s corporate infrastructure originating from China that resulted in the theft of intellectual property back in early 2010.
Therefore, when CISOs transparently talk about their findings (which may not happen often due to security reasons!), people will listen (see Yahoo! CISO, Justin Somaini’s, survey on Information Security Function, Governance and Risk Management, Culture and Communication, Metrics and KPI’s).
Security Analysts
Lastly, we surveyed over 75 of the top security analysts with the top 10 having voices which ranged from 347 to 710 times the average person. This is no surprise when you see analysts like Gartner’s Neil MacDonald openly discussing sensitive topics like what RSA did wrong following the SecurID breach earlier this year.
The Most Powerful Voices in Security
(see the table below infographic for #1 – #100)
The Rest of the Top 100
Keep in mind the rankings are relative to the others on the list. That means everyone on the list has a much higher criteria impact than the average active person. Also, note that most of the dimensions that make up the MPV are from the past 90 days.
Our study included over 140 security company executives, 320 bloggers and people in media, 100 of the top people in cloud computing, 30 people involved in specialized organizations like IBM’s X-Force, over 20 government officials, over 130 leading CISOs, and 75 industry analysts from notable firms such as Gartner, IDC, Forrester, ESG, and others. In total we researched over 800 people.
Please note that our ranking is not the final word on the subject, but the beginning of a discussion. For example, a Director at Symantec (who will remain anonymous) assisted us in double-checking our work, and couldn’t help but be of the opinion that Enrique Salem, Steve Trilling, and Rowan Trollope belong as 1-3 on every list (lol). So why isn’t Michael DeCesare or George Kurtz from McAfee on the list? Eva Chen from Trend Micro? Harriet P. Pearson, Nick Coleman, or Phil Neray from IBM? Did we miss anyone? You maybe? What did we get wrong? Please give us your thoughts by commenting below.
Other MPV Criteria
Must be an active social media individual now (Buzz metrics were taken from last 90 days).
We included corporate twitter accounts only when it was clear that it represents the voice of the individual.
They are known to speak on topics within the security community.
We removed irrelevant hits where necessary such as those for similarly-named individuals.
We’re defining the average active person as an active Internet user with an average level of impact, influence and use of social tools.
Next Steps
Are you wondering why some people made it on the Top 100 when they have less to do with security than others who didn’t? We hypothesize that a strong voice (who is not a security expert) can actually speak to an audience who does care about security. In this case, they could be more useful than a week voice (who is an expert). Sure, we want to follow the experts and thought leaders to gather further domain knowledge, trends, and vision. But lets say that we would like to challenge the status quo on a security topic in the cloud computing space. Do we engage Eugene Kaspersky on the topic? Maybe, or maybe we engage Paul Miller. In a future study, we will discuss how to further leverage your network of the influencers.
Be Proud If You Are In a Top Category
Are you one of the “Most Powerful Voices in Security”?
Add a note or badge (see below) to your website or blog to let people know that you are one of the most powerful voices in the security community.
Follow some of the more vocal security voices by automatically adding our twitter list here.
About The Author
Jim Kaskade is a CEO of ten years. Most recently serving as SVP and General Manager at SIOS Technology, a publicly traded firm in Japan, where he led a business unit focused on developing private cloud Platform as a Service targeted for Fortune 500 enterprises. Jim has been heavily involved in all aspects of security as it applies to the cloud, meeting with prominent CIOs and CISOs of Fortune 100 companies to better understand their cloud security needs. He also has direct security domain knowledge from his experience as founder and CEO of a SaaS company, which secured the digital media assets of over 10,000 businesses including Fortune 100 customers such as Lucasfilm, the NBA, Sony BMG, News Corp, Viacom, and IAC. Jim is also one of the Top 100 bloggers on Cloud Computing selected by the Cloud Computing Journal.











Jim – looks like ulitzer and sys-con unpublished your article – what’s up with that?